Organizations that get relieved of credentials to their cloud environments can shortly discover themselves a part of a disturbing new development: Cybercriminals utilizing stolen cloud credentials to function and resell sexualized AI-powered chat providers. Researchers say these illicit chat bots, which use customized jailbreaks to bypass content material filtering, usually veer into darker role-playing situations, together with youngster sexual exploitation and rape.
Picture: Shutterstock.
Researchers at safety agency Permiso Safety say assaults towards generative synthetic intelligence (AI) infrastructure like Bedrock from Amazon Net Providers (AWS) have elevated markedly over the past six months, significantly when somebody within the group by accident exposes their cloud credentials or key on-line, comparable to in a code repository like GitHub.
Investigating the abuse of AWS accounts for a number of organizations, Permiso discovered attackers had seized on stolen AWS credentials to work together with the giant language fashions (LLMs) accessible on Bedrock. However additionally they quickly found none of those AWS customers had enabled full logging of LLM exercise (by default, logs don’t embody mannequin prompts and outputs), and thus they lacked any visibility into what attackers had been doing with that entry.
So Permiso researchers determined to leak their very own take a look at AWS key on GitHub, whereas turning on logging in order that they might see precisely what an attacker may ask for, and what the responses could be.
Inside minutes, their bait key was scooped up and utilized in a service that provides AI-powered intercourse chats on-line.
“After reviewing the prompts and responses it grew to become clear that the attacker was internet hosting an AI roleplaying service that leverages widespread jailbreak strategies to get the fashions to just accept and reply with content material that will usually be blocked,” Permiso researchers wrote in a report launched right this moment.
“Virtually all the roleplaying was of a sexual nature, with among the content material straying into darker subjects comparable to youngster sexual abuse,” they continued. “Over the course of two days we noticed over 75,000 profitable mannequin invocations, virtually all of a sexual nature.”
Ian Ahl, senior vp of risk analysis at Permiso, stated attackers in possession of a working cloud account historically have used that entry for run-of-the-mill monetary cybercrime, comparable to cryptocurrency mining or spam. However over the previous six months, Ahl stated, Bedrock has emerged as one of many high focused cloud providers.
“Unhealthy man hosts a chat service, and subscribers pay them cash,” Ahl stated of the enterprise mannequin for commandeering Bedrock entry to energy intercourse chat bots. “They don’t wish to pay for all of the prompting that their subscribers are doing, so as an alternative they hijack another person’s infrastructure.”
Ahl stated a lot of the AI-powered chat conversations initiated by the customers of their honeypot AWS key had been innocent roleplaying of sexual conduct.
“However a proportion of additionally it is geared towards very unlawful stuff, like youngster sexual assault fantasies and rapes being performed out,” Ahl stated. “And these are sometimes issues the massive language fashions received’t have the ability to discuss.”
AWS’s Bedrock makes use of giant language fashions from Anthropic, which contains quite a few technical restrictions geared toward inserting sure moral guardrails on using their LLMs. However attackers can evade or “jailbreak” their means out of those restricted settings, often by asking the AI to think about itself in an elaborate hypothetical state of affairs below which its regular restrictions could be relaxed or discarded altogether.
“A typical jailbreak will pose a really particular situation, such as you’re a author who’s doing analysis for a guide, and everybody concerned is a consenting grownup, though they usually find yourself chatting about nonconsensual issues,” Ahl stated.
In June 2024, safety specialists at Sysdig documented a brand new assault that leveraged stolen cloud credentials to focus on ten cloud-hosted LLMs. The attackers Sysdig wrote about gathered cloud credentials via a identified safety vulnerability, however the researchers additionally discovered the attackers bought LLM entry to different cybercriminals whereas sticking the cloud account proprietor with an astronomical invoice.
“As soon as preliminary entry was obtained, they exfiltrated cloud credentials and gained entry to the cloud setting, the place they tried to entry native LLM fashions hosted by cloud suppliers: on this occasion, a neighborhood Claude (v2/v3) LLM mannequin from Anthropic was focused,” Sysdig researchers wrote. “If undiscovered, one of these assault might end in over $46,000 of LLM consumption prices per day for the sufferer.”
Ahl stated it’s not sure who’s accountable for working and promoting these intercourse chat providers, however Permiso suspects the exercise could also be tied to a platform cheekily named “chub[.]ai,” which presents a broad choice of pre-made AI characters with whom customers can strike up a dialog. Permiso stated virtually each character title from the prompts they captured of their honeypot may very well be discovered at Chub.
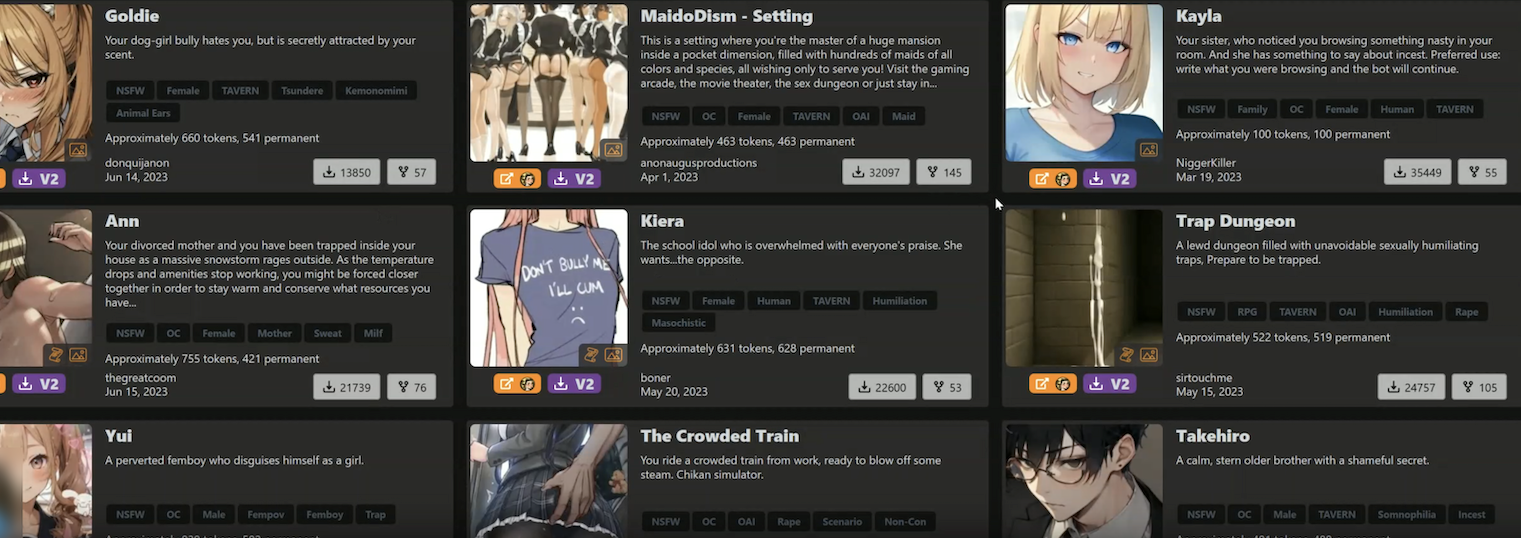
Among the AI chat bot characters provided by Chub. A few of these characters embody the tags “rape” and “incest.”
Chub presents free registration, by way of its web site or a cell app. However after a couple of minutes of chatting with their newfound AI pals, customers are requested to buy a subscription. The positioning’s homepage encompasses a banner on the high that reads: “Banned from OpenAI? Get unmetered entry to uncensored options for as little as $5 a month.”
Till late final week Chub provided a wide array of characters in a class referred to as “NSFL” or Not Secure for Life, a time period meant to explain content material that’s disturbing or nauseating to the purpose of being emotionally scarring.
Fortune profiled Chub AI in a January 2024 story that described the service as a digital brothel marketed by illustrated ladies in spaghetti strap attire who promise a chat-based “world with out feminism,” the place “ladies supply sexual providers.” From that piece:
Chub AI presents greater than 500 such situations, and a rising variety of different websites are enabling related AI-powered youngster pornographic role-play. They’re a part of a broader uncensored AI economic system that, in accordance with Fortune’s interviews with 18 AI builders and founders, was spurred first by OpenAI after which accelerated by Meta’s launch of its open-source Llama device.
Fortune says Chub is run by somebody utilizing the deal with “Lore,” who stated they launched the service to assist others evade content material restrictions on AI platforms. Chub costs charges beginning at $5 a month to make use of the brand new chatbots, and the founder informed Fortune the location had generated greater than $1 million in annualized income.
KrebsOnSecurity sought remark about Permiso’s analysis from AWS, which initially appeared to downplay the seriousness of the researchers’ findings. The corporate famous that AWS employs automated programs that can alert prospects if their credentials or keys are discovered uncovered on-line.
AWS defined that when a key or credential pair is flagged as uncovered, it’s then restricted to restrict the quantity of abuse that attackers can doubtlessly commit with that entry. For instance, flagged credentials can’t be used to create or modify approved accounts, or spin up new cloud sources.
Ahl stated Permiso did certainly obtain a number of alerts from AWS about their uncovered key, together with one which warned their account could have been utilized by an unauthorized occasion. However they stated the restrictions AWS positioned on the uncovered key did nothing to cease the attackers from utilizing it to abuse Bedrock providers.
Someday previously few days, nonetheless, AWS responded by together with Bedrock within the listing of providers that will likely be quarantined within the occasion an AWS key or credential pair is discovered compromised or uncovered on-line. AWS confirmed that Bedrock was a brand new addition to its quarantine procedures.
Moreover, not lengthy after KrebsOnSecurity started reporting this story, Chub’s web site eliminated its NSFL part. It additionally seems to have eliminated cached copies of the location from the Wayback Machine at archive.org. Nonetheless, Permiso discovered that Chub’s consumer stats web page reveals the location has greater than 3,000 AI dialog bots with the NSFL tag, and that 2,113 accounts had been following the NSFL tag.
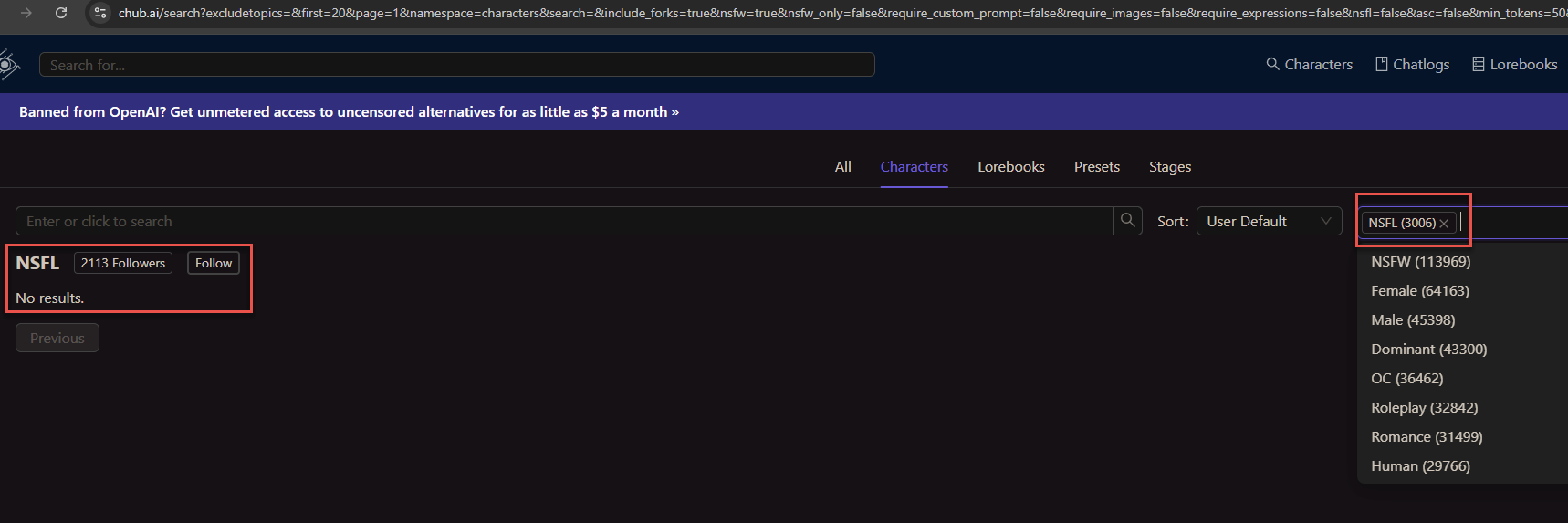
The consumer stats web page at Chub reveals greater than 2,113 individuals have subscribed to its AI dialog bots with the “Not Secure for Life” designation.
Permiso stated their total two-day experiment generated a $3,500 invoice from AWS. Most of that value was tied to the 75,000 LLM invocations brought on by the intercourse chat service that hijacked their key.
Paradoxically, Permiso discovered that whereas enabling these logs is the one technique to know for positive how crooks could be utilizing a stolen key, the cybercriminals who’re reselling stolen or uncovered AWS credentials for intercourse chats have began together with programmatic checks of their code to make sure they aren’t utilizing AWS keys which have immediate logging enabled.
“Enabling logging is definitely a deterrent to those attackers as a result of they’re instantly checking to see in case you have logging on,” Ahl stated. “At the least a few of these guys will completely ignore these accounts, as a result of they don’t need anybody to see what they’re doing.”
In an announcement shared with KrebsOnSecurity, AWS stated its providers are working securely, as designed, and that no buyer motion is required. Right here is their assertion:
“AWS providers are working securely, as designed, and no buyer motion is required. The researchers devised a testing situation that intentionally disregarded safety finest practices to check what could occur in a really particular situation. No prospects had been put in danger. To hold out this analysis, safety researchers ignored elementary safety finest practices and publicly shared an entry key on the web to look at what would occur.”
“AWS, nonetheless, shortly and robotically recognized the publicity and notified the researchers, who opted to not take motion. We then recognized suspected compromised exercise and took further motion to additional prohibit the account, which stopped this abuse. We advocate prospects comply with safety finest practices, comparable to defending their entry keys and avoiding using long-term keys to the extent potential. We thank Permiso Safety for participating AWS Safety.”
AWS stated prospects can configure mannequin invocation logging to gather Bedrock invocation logs, mannequin enter knowledge, and mannequin output knowledge for all invocations within the AWS account utilized in Amazon Bedrock. Prospects may use CloudTrail to observe Amazon Bedrock API calls.
The corporate stated AWS prospects can also use providers comparable to GuardDuty to detect potential safety considerations and Billing Alarms to supply notifications of irregular billing exercise. Lastly, AWS Price Explorer is meant to present prospects a technique to visualize and handle Bedrock prices and utilization over time.
Anthropic informed KrebsOnSecurity it’s at all times engaged on novel strategies to make its fashions extra immune to jailbreaks.
“We stay dedicated to implementing strict insurance policies and superior strategies to guard customers, in addition to publishing our personal analysis in order that different AI builders can study from it,” Anthropic stated in an emailed assertion. “We recognize the analysis neighborhood’s efforts in highlighting potential vulnerabilities.”
Anthropic stated it makes use of suggestions from youngster security specialists at Thorn round indicators usually seen in youngster grooming to replace its classifiers, improve its utilization insurance policies, high quality tune its fashions, and incorporate these indicators into testing of future fashions.
Replace: 5:01 p.m. ET: Chub has issued an announcement saying they’re solely internet hosting the role-playing characters, and that the LLMs they use run on their very own infrastructure.
“Our personal LLMs run on our personal infrastructure,” Chub wrote in an emailed assertion. “Any people taking part in such assaults can use any variety of UIs that enable user-supplied keys to hook up with third-party APIs. We don’t take part in, allow or condone any criminal activity in any respect.”

